Variable Pay
What is variable pay?
Variable pay is a compensation structure where a portion of an employee’s earnings is tied to performance, results, or achieving specific goals, rather than being guaranteed as part of a fixed salary or hourly wage. It is designed to motivate employees to meet or exceed set goals, and is often used to align their efforts with organizational objectives.
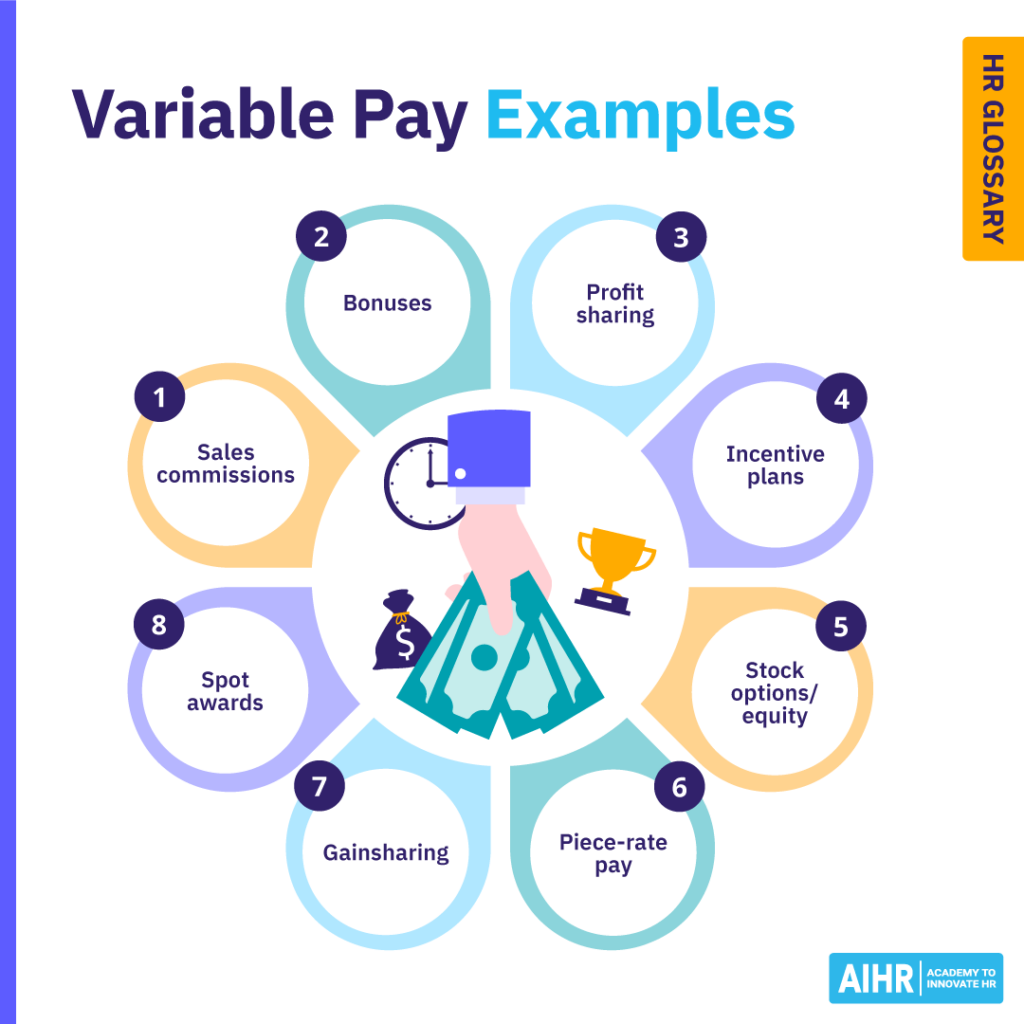
Variable pay examples
Here are some examples of variable pay:
- Commission: Sales professionals often earn a percentage of their revenue, which encourages higher performance.
- Bonuses:
- Performance bonuses: Reward employees based on achieving individual or team goals.
- Sign-on bonuses: Offered to attract new hires, especially for hard-to-fill positions.
- Retention bonuses: Given to encourage employees to stay during critical periods.
- Profit-sharing: Employees receive a share of the company’s profits, typically based on the organization’s financial performance.
- Incentive plans:
- Project-based incentives: Rewards tied to the successful completion of specific projects.
- Team-based incentives: Offered when teams achieve predefined goals.
- Stock options/equity: Grants employees the right to purchase company shares at a set price, often used in startups or senior-level positions.
- Piece-rate pay: Compensation based on the quantity of work completed, common in manufacturing or freelance work.
- Gainsharing: Employees receive a bonus if they collectively improve efficiency or reduce costs in their work processes.
- Spot awards: On-the-spot rewards for exceptional contributions or achievements.
Types of variable pay
1. Individual
This type is tied directly to an individual’s efforts and performance. It establishes a clear link between an employee’s work and their reward. Examples include:
- Piece-rate pay: Earnings based on the number of units produced.
- Bonuses: One-time payments for exceptional individual performance.
- Special incentive programs: Includes cash rewards or recognition awards.
- Sales compensation: Payment based on a percentage of sales revenue.
2. Group/team
This involves rewarding a team for collective performance. It promotes collaboration, often distributing rewards equally or based on contributions. Some examples include:
- Gainsharing: A self-funded program where employees share measurable financial gains from improved productivity, efficiency, or cost reductions.
- Goalsharing: Rewards based on achieving organizational or team-wide goals, such as improving customer satisfaction. Unlike gainsharing, it is not self-funded.
3. Organizational
This type is linked to the company’s overall success and is designed to enhance morale and organizational performance. Examples include:
- Profit-sharing: Distributing profits among employees.
- Employee stock plans: Offering company shares as a reward.
- Executive stock options: Equity-based rewards for leadership roles.
- Deferred compensation: Future payments based on performance or tenure.

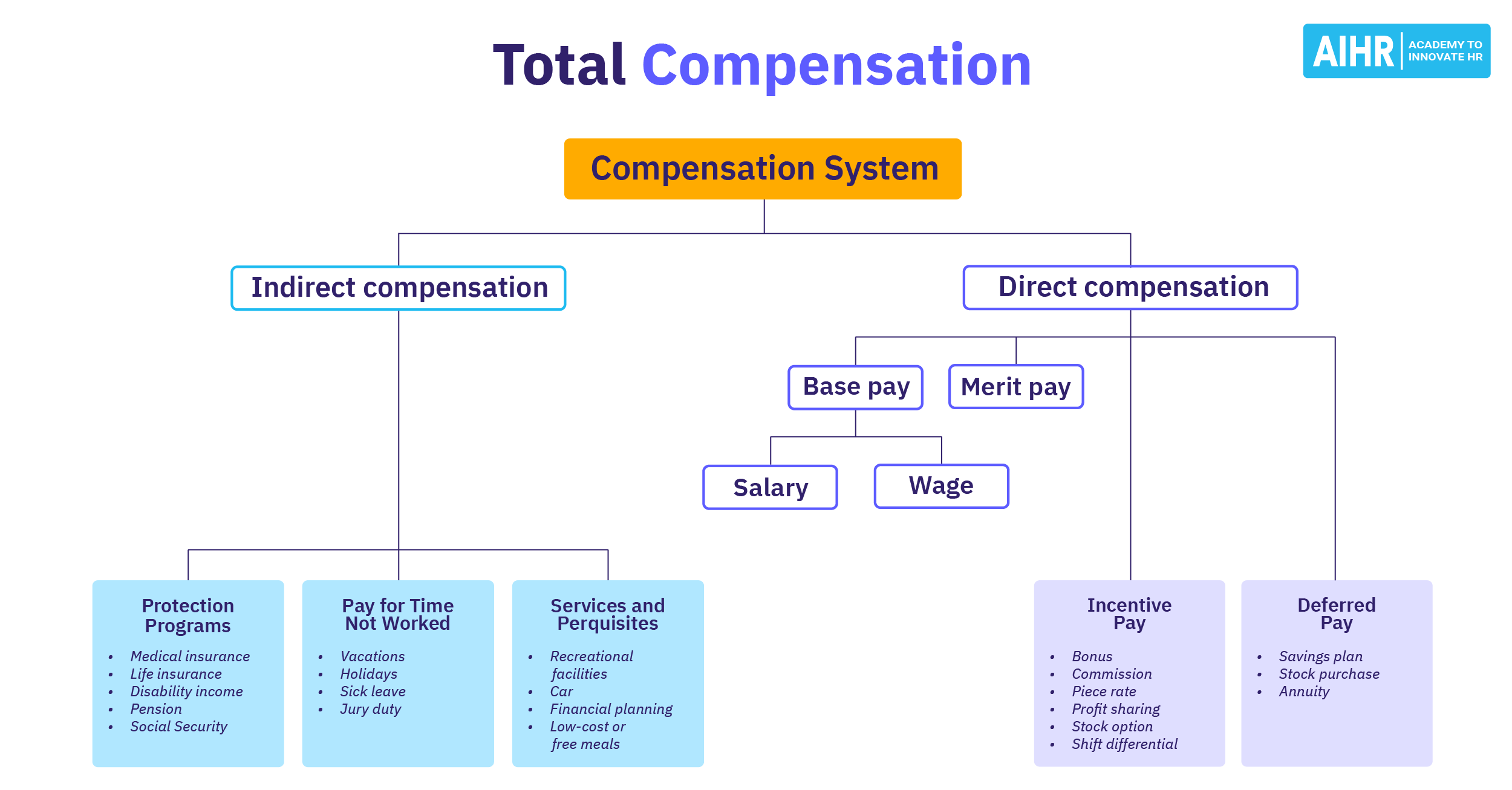
Base pay vs. variable pay
The distinction between base pay and variable pay lies in how the compensation is structured and what factors determine it:
Definition
Fixed compensation for fulfilling job requirements.
Compensation tied to performance, results, or specific goals.
Purpose
Provides financial stability and a foundation for earnings.
Motivates and rewards individual, team, or organizational achievements.
Stability
Guaranteed and predictable.
Fluctuates based on outcomes or performance.
Payment frequency
Paid regularly (e.g., bi-weekly or monthly).
Paid at intervals, often tied to milestones (e.g., quarterly bonuses).
Examples
Salary, hourly wages, or contractual rates.
Performance bonuses, commissions, profit-sharing, and stock options.
Fixed pay vs. variable pay
Fixed pay and variable pay are two key components of compensation, each serving a distinct purpose.
Fixed pay is the guaranteed portion of an employee’s earnings, such as a salary or hourly wage. It is predictable, consistent, and unrelated to performance, providing financial stability for the employee. This type of pay reflects the value of the role and the employee’s skills or experience.
On the other hand, variable pay depends on achieving specific goals or results. This flexible component includes bonuses, commissions, and profit-sharing, serving as an incentive to drive success and align individual efforts with organizational objectives.
In essence, fixed pay ensures stability, while variable pay motivates performance, offering a balanced approach to compensation.
Advantages and disadvantages of variable pay
Advantages
- Motivates performance: A well-structured variable pay plan incentivizes employees to achieve individual, team, or organizational goals.
- Cost-effective: Organizations pay more for exceptional performance and save costs during low-performance periods.
- Rewards high performers: Differentiates top performers through greater rewards, boosting engagement and retention.
- Flexibility for employers: Companies can adjust variable pay programs based on financial performance or market conditions.
Disadvantages
- Unpredictability for employees: Variable earnings can lead to financial uncertainty, especially if performance targets are challenging to meet.
- Potential for unhealthy competition: Individual performance incentives may discourage teamwork or create conflicts among employees.
- Risk of misalignment: If poorly designed, variable pay systems may incentivize the wrong behaviors (e.g., short-term results over long-term sustainability).
- Overemphasis on pay: Employees may focus solely on achieving incentives rather than other aspects of their role, such as collaboration or quality.
How HR can implement a variable pay plan
Implementing a variable pay plan involves several strategic steps to align it with organizational goals and ensure its effectiveness. Here’s a concise guide:
- Define objectives: Clearly articulate the goals of the plan. Common objectives include improving individual or team performance, aligning employee efforts with organizational priorities, or driving specific outcomes like cost savings or revenue growth.
- Understand the workforce: Evaluate the roles and responsibilities within the organization to determine which positions would benefit most from this kind of pay. This could include roles with measurable outcomes, like sales or customer service.
- Design the pay plan: Consider the following:
- Choose a structure: Decide on the variable pay structure, such as bonuses, profit-sharing, commissions, or performance-based incentives.
- Set clear criteria: Establish measurable metrics, such as sales targets, customer satisfaction scores, or project milestones, that tie directly to the organization’s goals.
- Decide frequency: Establish how often payouts will occur—monthly, quarterly, or annually.
- Implement and monitor: Roll out the plan organization-wide. Regularly monitor its impact on performance and employee engagement, adjusting metrics or payouts as needed to maintain alignment with business goals.
FAQ
Variable pay is a type of compensation based on performance or results, rather than a fixed salary. It includes bonuses, commissions, profit-sharing, or incentives tied to individual, team, or company achievements.
An example of a variable pay plan is a sales commission program, where employees earn a percentage of the revenue they generate in addition to their base salary. Other examples include annual performance bonuses or profit-sharing plans.
A bonus is a one-time reward given for achieving specific goals or milestones, while variable pay is a broader term that includes all performance-based compensation, such as bonuses, commissions, and profit-sharing.
Variable pay is compensation tied to performance or results, such as bonuses, commissions, or profit-sharing. It fluctuates based on achieving specific goals.
Non-variable pay (also known as fixed pay) is a predetermined amount, such as a salary or hourly wage, that remains consistent regardless of performance.